The Bittensor Security Playbook (Max Safety, Zero Paranoia)
Protecting your TAO without burying it in the woods
Two years ago, I sent a decent amount of Ethereum from my wallet to a major exchange. It was a verified address I had used many times before. I had it saved.
I didn’t check if it was up to date.
I clicked confirm. Then I went to make coffee.
When I came back to my desk, I refreshed the exchange. Nothing.
That’s when the cold feeling started spreading from my chest outward.
I pulled up the transaction hash. Confirmed on the blockchain. The ETH had definitely left my wallet. It had gone somewhere.
The exchange had upgraded their security infrastructure and rotated their deposit addresses. My ETH had gone straight into the void, not to a scammer, just to an address that no longer existed in their system.
My hands went numb. There’s no emergency undo button in crypto. Just me, a blockchain that doesn’t care, and an exchange support ticket system that takes an age to respond.
Cue a very nervous couple of weeks checking my email every few hours, imagining explaining to my wife that I’d basically thrown thousands of dollars into a digital trash can.
When the support team finally replied saying they had manually retrieved the funds, I actually stood up from my desk. The relief was physical.
It was a very lucky escape.
Now picture that same scenario, but with your TAO and this time there is no exchange involved. There’s no customer support to email. No manual retrieval. The blockchain is immutable and the funds are just gone.
Most crypto losses are simple human mistakes. We obsess over the technology—hardware wallets, encryption, multi-sig—while completely ignoring the human element that leaves the back door wide open.
This is especially true here. Bittensor is a machine intelligence network.
But it runs on a blockchain.
You might be here purely for the AI, but the underlying plumbing is crypto. Even if you don’t care about DeFi or web3, if you hold TAO, you are operating in a crypto-adjacent world. And that means we have to adopt their security practices to protect our assets.
So lets make sure we don’t lose them.
Why Security Actually Matters (Beyond Fear)
The reason we’re obsessing over security isn’t because TAO is doomed to be stolen. It’s because TAO is worth securing.
You’re protecting your stake in the only decentralized AI network that’s actually working. You’re protecting a bet that monopoly AI eventually annoys enough people that alternatives become valuable.
And if you follow three boring steps: offline seed phrase, isolated environment, routine checks—you’re already in the top 10% of secure holders. The bar is shockingly low.
Don’t think that because TAO is trading at $200 as I write this, security doesn’t matter yet. What happens when it’s 10x from here? Or 30x? You know the network has that potential.
You need to treat your TAO like it’s worth what it could be in 5-10 years, not what it’s worth today.
Remember the guy who threw away a hard drive containing thousands of BTC? It’s sitting in a UK landfill right now, now worth hundreds of millions of dollars. He was careless when Bitcoin felt like Monopoly money.
We don’t want to be that person in 2035, frantically trying to remember what happened with our TAO that was casually bought and lost.
How Bittensor Guru Got Duped
Because scammers can’t hack the Bittensor blockchain, they don’t even try. Instead, they try to hack you.
Right now, the number one social engineering threat in crypto is Social Media DMs.
Take Keith Singery’s story. Better known as Bittensor Guru, Keith is a sharp, early Bittensor validator who lived in the Discords and codebases every day.
He understood the tech, the risks, the culture. And he still lost over 5,400 TAO ($300k+) to a Discord impersonator.
Keith was running a Bittensor validator and holding others’ TAO on his cold wallet. In early 2023, a scammer impersonated one of his delegators and tricked him into sending TAO to the wrong address.
He’d normally double‑check via a second channel, but skipped his usual checks that morning. The scammer had reused an old DM, changed their name and avatar to match the real user, and mimicked their writing style.
After the loss, Keith tightened his security, removed most third‑party funds from his validator and took an extended break from the ecosystem.
This is where the reality hits. There is nobody to call if you mess up.
We have to build systems that guard against the stupidest, most tired versions of ourselves.
The Threats You Actually Face
Let’s strip away the complexity of what a wallet actually is.
At its core, a wallet is just two things:
A public key: Your routing number. It’s how people send you funds.
A private key/seed phrase: The master vault combination. It gives total control.
The cardinal rule of crypto is that your seed phrase never touches a screenshot, a cloud note, or a random Wi-Fi printer. You write it on paper or engrave it on metal. You never copy-paste it into a chat box.
(For a deeper dive on which specific wallets to use, check out The 2026 Guide to Bittensor Wallets).
Now let’s break down what you’re really defending against, because abstract security advice doesn’t stick:
Social Engineering (Discord DMs, Fake Upgrades):
How it works: Someone impersonates a validator, subnet owner, or support rep. They convince you to send funds to their address. Or they send you a link to “upgrade your wallet.” You enter your seed phrase. They drain your wallet.
Real example: Keith Singery lost 5,400 TAO this way despite being deeply technical.
Defense: Only use your seed phrase if the idea originated with you. Never click links in DMs. Reach staking sites via your own bookmarks. Don’t rely on Google search results, which are frequently hijacked by malicious ads.
Operational Mistakes (Wrong Address, Fat-Finger Errors):
How it works: You send TAO to the wrong address (typo, outdated saved address, wrong network). The blockchain doesn’t care that you made a mistake—the transaction is final.
Real example: My ETH exchange mistake from earlier.
Defense: Verify every character, send test amounts first, never rush.
Theft (Seed Phrase Compromise):
How it works: Your seed phrase gets photographed, screenshotted, saved in cloud notes, or typed into a compromised device. Someone finds it and drains your wallet while you sleep.
Real example: Countless “I lost everything” posts where people stored seeds digitally.
Defense: Seed phrases never touch screens. Paper or metal only.
Environment Risk (Compromised Device, Malware):
How it works: You use a wallet on a device loaded with malware, keyloggers, or malicious browser extensions. Even without your seed, sophisticated attacks can trick you into signing malicious transactions.
Real example: Browser extension scams that clone legitimate wallet interfaces.
Defense: Dedicated device or isolated browser profile for your TAO activity only.
The Framework: The 3-Tier TAO Setup
Bittensor’s blockchain architecture actually gives us a massive advantage: the coldkey and the hotkey.
Think of your coldkey as your identity. It’s your vault. It holds the power. Think of your hotkey as a worker badge. It goes out, does the daily work on subnets, and can be replaced if lost.
Each tier below addresses specific threats and gives you concrete defenses.
Pick your lane:
1) The Everyday Participant (Low-Medium Holdings)
You hold TAO, delegate, and don’t run miners yourself.
The Setup:
Keep your serious TAO on one main hardware wallet (Ledger + Crucible/Talisman/TAO.com/Nova)
Set up a “burner” browser wallet with smaller amounts for playing with subnets
Seed phrase: Handwritten on paper, stored in fireproof safe at home
Environment: Dedicated browser profile for crypto only (no shopping, no random extensions)
Threats This Solves:
✅ Phishing: Your serious stack never touches the internet
✅ Operational mistakes: Test transactions happen in burner wallet first
✅ Environment risk: Isolated browser means malware can’t see your main wallet
If all you do after reading this piece is separate “experiment TAO” from “serious TAO”, you’ve already upgraded.
2) The Active Operator (Miners / Validators / Builders)
You run miners, validate, and interact with subnets frequently.
The Setup:
Coldkey: Hardware wallet, never touches servers. Only signs big moves (staking, redelegating, withdrawals)
Hotkeys: Live on your servers, funded minimally
Seed phrase: Split storage: one copy at home, one copy in safe deposit box
Transaction verification: Every coldkey transaction gets verified on two different devices before signing
Threats This Solves:
✅ Theft: Even if your server is compromised, attacker can’t access coldkey
✅ Operational mistakes: Dual-device verification catches wrong addresses
✅ Social engineering: Your process doesn’t allow rushing as verification takes time
Move slow and carefully with the coldkey. Move fast with hotkeys. Never keep more power on the hotkey than absolutely necessary.
3) The High-Stakes Holder
You have significant TAO and a multi-year horizon.
The Setup:
Primary: Hardware wallet, never touches servers
Seed phrase: Written on metal (like Cryptosteel), stored in two separate physical locations (bank deposit box and one other location)
Environment: Dedicated laptop for TAO only, never used for email/browsing/downloads
SOP document: Written instructions for every fund movement, stored separately from seed
Recovery test: Annual test recovery with small wallet to ensure process still works
Threats This Solves:
✅ All of the above, plus...
✅ Physical disaster: Fire/flood can’t destroy both seed copies
✅ Death/incapacity: Your family can access funds with clear instructions
✅ Memory failure: 5 years from now, you remember the process because it’s documented
If your future self finds your setup obvious and dull, you’ve done it right. Boring is good.
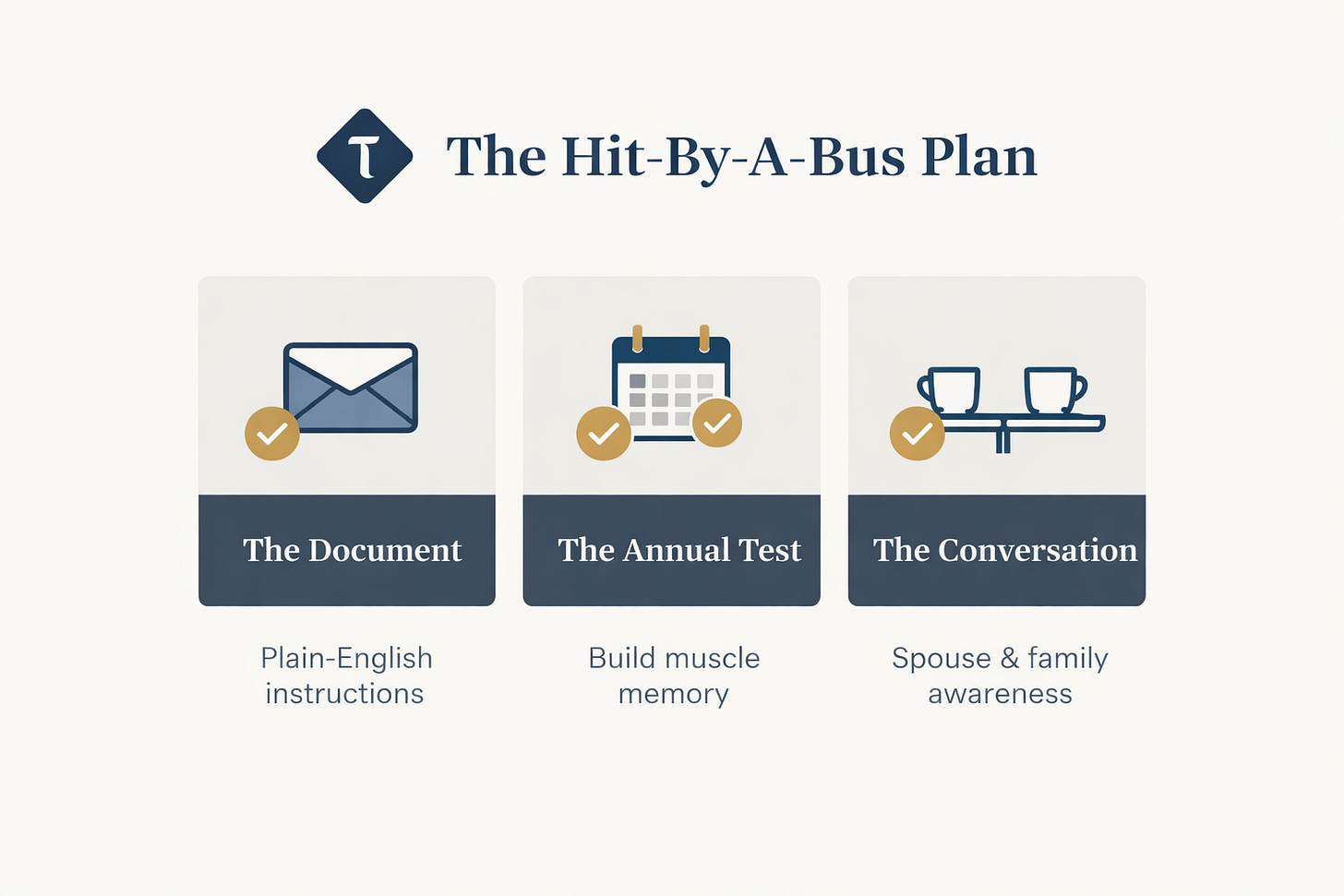
The Hit-By-A-Bus Plan
This is the big gap in most security guides.
What happens if you vanish tomorrow?
Don’t build a fortress so strong that your own family can’t get in. As Pamela Morgan says in her seminal work Cryptoasset Inheritance Planning: you need a clear, boring backup process.
Design recovery for:
Forgotten password but seed still safe
Device lost or stolen
One copy of seed damaged (fire, water, etc.)
Death/incapacity: can anyone you trust eventually access funds?
What I’ve actually implemented:
The Recovery Document (stored separately from seed):
“If something happens to me, here’s what TAO is and why it matters”
Exact locations of all seed phrase copies (e.g. home safe, bank deposit box)
Step-by-step wallet recovery instructions in non-technical language
Contact info for two trusted helpers.
The Annual Test:
Once a year or so, I set up a fresh wallet with a small amount of crypto
Intentionally wipe it
Recover it from seed phrase following my own instructions
This ensures: (a) my seeds still work, (b) my instructions are clear, (c) the process is muscle memory
The Conversation:
I’ve walked my wife through the recovery document once
She knows where it is
She knows it exists
She doesn’t need to understand subnet emissions, just how to access the value if I’m gone
This may sound like overkill, but it gives you peace of mind. The best time to practice recovery is when nothing is on fire.
Adversarial By Design
Bittensor expects bad actors.
The entire protocol is designed assuming every participant is trying to game the system. In fact, the ecosystem treats exploiters as the best red-team testers. People are implicitly paid to break things so the protocol can harden.
If the protocol evolves under adversarial pressure, we have to do the same. Not with paranoia, but with preparation.
Pick exactly one thing from this issue and do it this week. Set up an experiment wallet. Buy a hardware wallet (Ledger for TAO compatibility). Write down your “Hit-By-A-Bus” plan.
Remember: Bittensor is an infinite game. You’re not trying to time the perfect exit, you’re trying to stay in the game long enough for the network to mature.
Security isn’t about being paranoid. It’s about being still holding TAO in 2030 when the rest of the world finally catches up.
Until next time.
Cheers,
Brian
Disclaimer: This is not financial advice. I am a writer documenting the Bittensor ecosystem. Always do your own research.




Beautiful article and it's something everyone needs to read. Everyday thousands of people make the switch from buying their first bit of Bitcoin, to exploring other tokens. As retail investors increase, the scammers are licking their chops!
6 months ago, I had a wallet drained of nearly $16,000 in strATEGY (eth). On Discord, someone compromised a moderator's account on an official crypto server, they made a very legitimate post, I connected my wallet and it was all over. One of the worse feelings I've ever experienced. Like you said, no one's calling and there's no one I can really call! Lidi.fi does not have a tech support number 🤣🤣
A lot of lessons were learned that day, thankfully I had taken the advice of AI, and used a different wallet for every type of coin I owned, so only one thing was compromised. Since then, it's all in a Ledger.
I'll say one thing, anyone into crypto can be victimized so they all need to be familiar with revoke.cash and DeBank!!
Great reality check. We spend so much time looking at the protocol that we forget social engineering is the real threat. Implementing the dedicated burner browser profile today. Appreciate the peace of mind!